Protecting Personal Data with Multi-Factor Authentication and Identity Proofing
The need for multiple factors of authentication in the current environment is something that many can agree on. But does that impact how we do web site authentication risk assessment? What other aspects of token and credential choice are impacted?

I am both fascinated and occasionally bemused by how folks sometimes make relatively simple things complex. So wanted to share how I am looking at this shift.
BTW, even the U.S. Government has gotten into the act with the recent Executive Order:
... ensure that all agencies making personal data accessible to citizens through digital applications require the use of multiple factors of authentication and an effective identity proofing process ...
EO on Improving the Security of Consumer Financial Transactions
[ While I am a civil servant in my job persona, I don’t live in the realm where the policy gods do battle. As such I do not have any special insight, input or visibility into executive orders or associated policies and implementation plans. These are, as always, my personal opinions and do not represent my employer’s view in any way. If you think it does, that would be … silly! ]
Determining risk posed by authentication errors
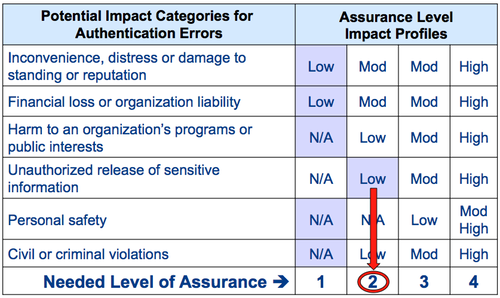
The typical evaluation sequence, based on OMB M-04-04 E-Authentication Guidance for Federal Agencies (PDF), involves conducting a risk assessment, mapping risks to an applicable assurance level impact profile, selecting appropriate credentials based on technical guidance and validating the system has met the required assurance level; rinse and repeat.
I’ve written extensively about this before, so won’t repeat it here, other than noting that the risk assessment process does not need to change, and that:
- Sensitive information (a.k.a. personal data) comes into the picture at impact level 2
- Requirement to identity proof comes into the picture at impact level 2
Credentials that can support the needed assurance level
Given the above, the changes that need to happen can be encapsulated in one simple statement:
Single factor credentials are no longer sufficient to mitigate the risks associated with a level 2 assurance level impact profile.
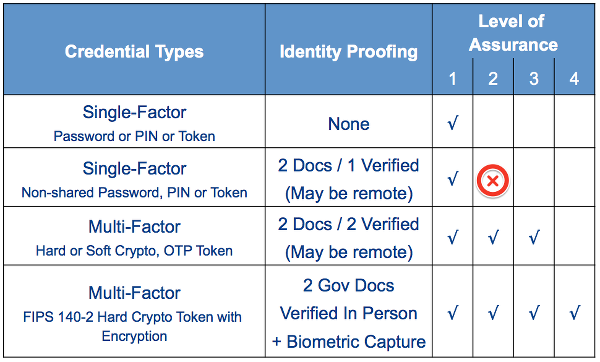
As always, details matter. So paying attention to the implementation details of multi-factor authentication will become particularly important.
RELATED INFO
- HOW-TO Conduct a Risk Assessment to Determine Acceptable Credentials
- Why Multi-Factor and Two-Factor Authentication May Not Be the Same
- U.S. Executive Order – Improving the Security of Consumer Financial Transactions
- OMB M-04-04 E-Authentication Guidance for Federal Agencies (PDF)
This blog post first appeared on Anil John | Blog (https://blog.aniljohn.com). The opinions expressed here are my own and do not represent my employer’s view in any way.




