The Missing Link Between Tokens and Identity
Component identity services, where specialists deliver services based on their expertise, is a reality in the current marketplace. At the same time, the current conversations on this topic seem to focus on the technical bits-n-bytes and not on responsibilities. This blog post is an attempt to take a step back and look at this topic through the lens of accountability.
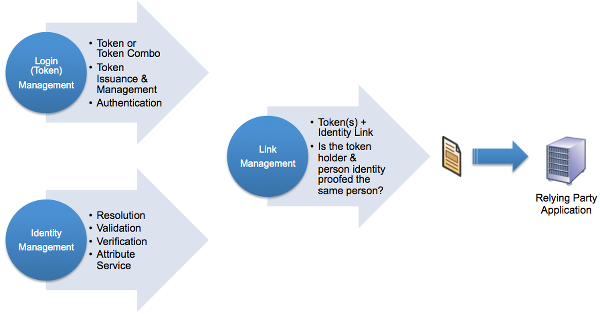
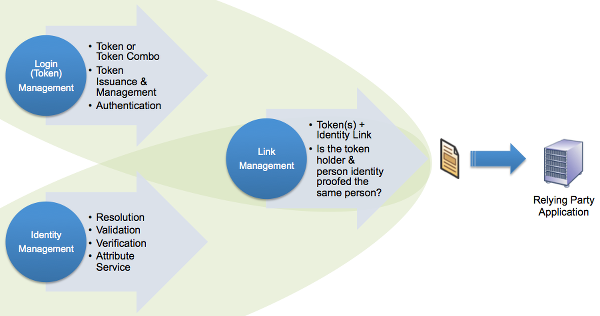
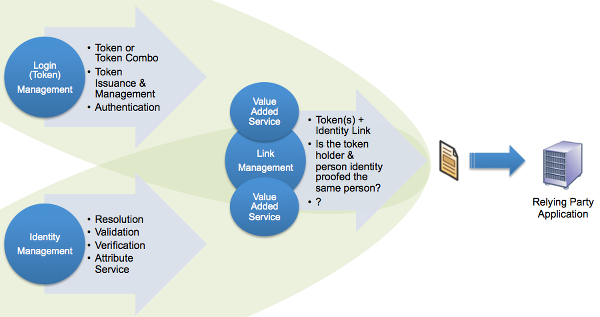
Login (Token) Management is a topic that is pretty well understood and to a great extent standardized. Yes, there will always be new token types coming into the market, but the process for evaluating them is in place. There is also increasing clarity around the identity management piece, and while there are many more moving pieces there, that piece is also maturing nicely.
What I find missing, or in the hand-waving phase, is the conversation around link management which I consider to be critically important in making the use of component identity services successful.
Link management, at a high level, covers two things:
- The strength and rigor of the process used to link (a.k.a. bind) the token(s) to an identity
- The strength and rigor of the process used to ensure that the token holder and the person who was identity proofed are the same person
At the end of the road, the RP is out-sourcing one or more management functions to another entity and holding it accountable to fulfill them in a manner the RP finds acceptable. As such, looking at the the various out-sourcing options through an accountability lens may be helpful in jump-starting the discussion.
Out-Sourcing Option 1:
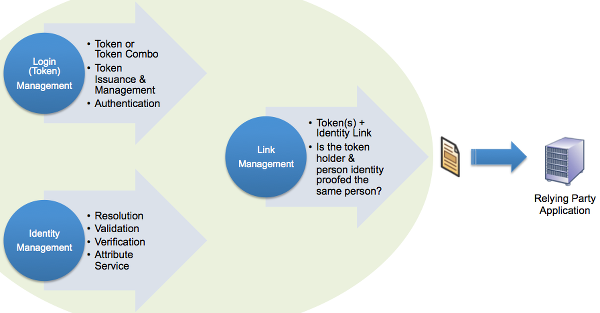 <div class=“table-responsive”>
<div class=“table-responsive”>
| Configuration | Accountability Considerations |
|---|---|
|
|
</div>
Out-Sourcing Option 2A:
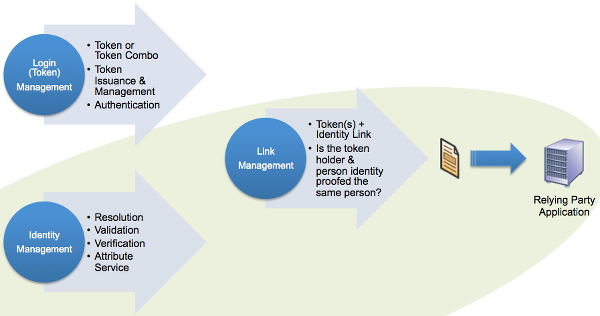 <div class=“table-responsive”>
<div class=“table-responsive”>
| Configuration | Accountability Considerations |
|---|---|
|
|
</div>
Out-Sourcing Option 2B:
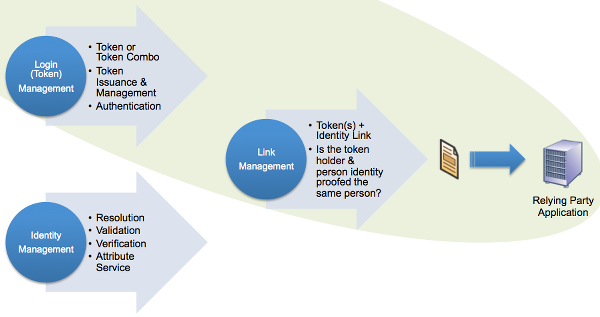 <div class=“table-responsive”>
<div class=“table-responsive”>
| Configuration | Accountability Considerations |
|---|---|
|
|
</div>
For all of the ambiguities around link management, the above three configurations are very much in play right now. That does not hold true to the following two options; cue excitement!
Out-Sourcing Option 3:
 <div class=“table-responsive”>
<div class=“table-responsive”>
| Configuration | Accountability Considerations |
|---|---|
|
|
</div>
Out-Sourcing Option 4:
 <div class=“table-responsive”>
<div class=“table-responsive”>
| Configuration | Accountability Considerations |
|---|---|
|
|
</div>
I tend to watch and listen, with an occasional sense of bemusement, the tit-for-tat conversations around certifications and trust-marks and self-attestations. At the end of the road, for certifications or self-attestations to have any value, it needs to be a proxy for allocation of responsibility and accountability when things go wrong. As such, looking at out-sourcing component identity services through an accountability lens may be the most effective way to get from point A to B.
Question: What value-added services can you see being offered by a Link Manager at higher levels of assurance?
RELATED INFO
- IDMGOV INFO: FICAM TFS Component Identity Services Terminology
- NIST SP-800-63-1 Multi-Token Assurance Level Matrix
- Identity Establishment, Verification and Validation
This blog post first appeared on Anil John | Blog (https://blog.aniljohn.com). The opinions expressed here are my own and do not represent my employer’s view in any way.




