Should Level of Assurance be Scalar or a Vector?
Levels of Identity Assurance continues to be one of the most discussed topics in the identity world. One of the oft-debated aspects is whether it should be conveyed as a singular number, distilled from an underlying set of components, or if the underlying set of components themselves should be conveyed.
Andrew Nash, in a twitter sidebar discussion during the recent Cloud Identity Summit, noted that 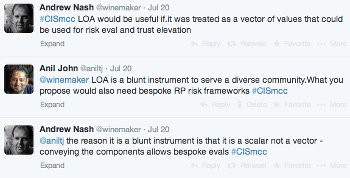 conveying the underlying components that make up LOA would enable them to “… be used for risk eval and trust elevation”.
conveying the underlying components that make up LOA would enable them to “… be used for risk eval and trust elevation”.
This is a point that Steve Wilson, who I hope to meet IRL one day, has championed as well (Attributes! Attributes! Attributes!).
In particular, I would encourage catching up on the discussion between Steve and Ken Dagg in the comments of Steve’s blog post on this topic.
In addition, I consider Eve Maler’s blog post on this topic to be just as relevant today as it was back in 2009!
My personal viewpoint on this is a blending of the ideas of the above folks with some additional seasoning:
- LOA, as a scalar, was designed to satisfy the requirements of a custom risk assessment framework of a specific vertical/community-of-interest, the U.S. Federal Government. It is, by its need to support a diverse community even within that vertical, at a coarse level of abstraction
- It would be a stretch of the imagination to assume that the risk assessment framework for a particular vertical/community-of-interest or in some cases, a specific RP, would apply equally well to another vertical/community-of-interest
- Given the uniqueness of each risk assessment framework and the corresponding results, there seem to be two ways to address this:
- Convey the underlying components of what goes into making up a LOA, and use that as input into an RP-driven, bespoke, risk assessment framework
- Use the scalar LOA value as a minimal common baseline, and have the RP put in its own compensating controls based on its unique/community-specific risk assessment
My sense is that the first approach will appeal to organizations with a nuanced and dynamic approach to risk mitigation, while the latter will appeal to those in regulated environments with a sophisticated understanding of risk and consequences. But note that both require that a risk assessment framework exist at the appropriate level of granularity.
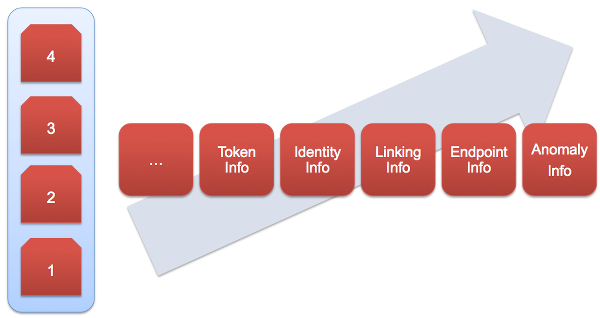
BTW, it is interesting to note that even though LOA is currently conveyed as a scalar number, it is actually the “low watermark” of the following components:
- Identity proofing and registration
- Issuance of token or combination of tokens
- Binding between identity proofing and tokens (if done separately)
- Token and credential management processes
- Authentication protocols
- Authentication assertions (if used)
At the same time, we do need to move from purely static components to incorporate continuous identity verification components as well. So, I keep wondering if the way forward is, in addition to the scalar LOA number, we should also find a way to convey the existing static components as well as additional continuous verification components. Then we can start the discussion on whether or not that representation should be a vector or a graph!
Question: Are there industry/vertical specific risk frameworks that incorporate identity assurance components?
RELATED INFO
- HOW-TO Conduct a Risk Assessment to Determine Acceptable Credentials
- Are Federated Credentials and Continuous Identity Verification Compatible
- Stephen Wilson: I just don’t get Levels of Assurance
- Eve Maler: How to rest assured
- These Are Not The LOAs (1+,2+,3+) You Are Looking For. Move Along
This blog post first appeared on Anil John | Blog (https://blog.aniljohn.com). The opinions expressed here are my own and do not represent my employer’s view in any way.




