Standardizing the RP Requirements for Identity Resolution
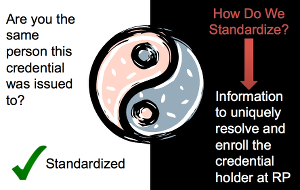
When a credential from an outsourced CSP shows up at the front door of a RP, the RP needs two pieces of information. First, an answer to the question “Are you the same person this credential was issued to?” and second, information to uniquely resolve and enroll the credential holder at the RP. We have more or less standardized the first bit, but have not been as mindful about the second.
 I have my own opinions as to why this has not been done before:
I have my own opinions as to why this has not been done before:
- This is typically a federation requirement, and successful federations exist in industry verticals where this is addressed by the operator of that closed community
- A driver for this requirement, e.g. public sector service delivery, where multi-sector standardization would have significant benefits has only recently started to come online
- Entities who, in the absence of RP access to authoritative identity establishment sources, have become gatekeepers to identity resolution may desire to protect their IP (“magic sauce”)
At the same time, I do believe that in order to deliver public sector services, it is critical to address this issue. But it needs to be done in a manner that looks at the world as it exists and not as we would wish it to be, which in the U.S. means that:
- There is little to no direct access to authoritative identity establishment sources
- Identity verification and validation are done by corroborating different sources of non-authoritative information
- Entities with IP (“magic sauce”) to bring to the table when dealing with that aggregated set of data have a role to play
- RP’s need a set of quantitative criteria to evaluate what they get from such an entity i.e. “identity proofing component”
To make this happen will require three things:
- A clear understanding by the RP of the various approaches it can utilize to enroll users
- An understanding of the context in which IP/proprietary approaches have a role in identity resolution e.g. At the “identity proofing component”
- Development and standardization of the quantitative criteria used by the RP to evaluate the information it needs for identity resolution
RELATED INFO
- Identity Establishment, Verification and Validation
- If You Don’t Plan For User Enrollment Now, You’ll Hate Federation Later. Redux.
- Context and Identity Resolution
- IDMGOV INFO: FICAM TFS TEM on Identity Resolution Needs for Online Service Delivery
This blog post first appeared on Anil John | Blog (https://blog.aniljohn.com). The opinions expressed here are my own and do not represent my employer’s view in any way.




