Tell Us Once or Tell Us Each Time; Implications for Digital Services
Delivering task based or transactional digital services requires paying close attention to user experience in identifying the customer while minimizing the amount of duplicative, error-prone data entry. At the same time, when a customer is interacting with an organization with independent business units or with multiple Government departments, a balance needs to be struck between convenience and creepiness when it comes to identity information collection and use. What are some of the factors that need to be considered when setting out on this path?
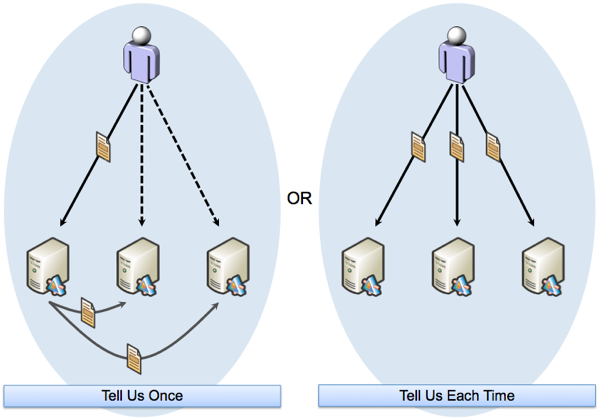
The term of art that is often used when this topic comes up is “Tell Us Once” as in “We want to implement a ‘tell us once’ strategy to improve the user experience”. The intent is if you have already provided some identity related (or other) information to an organization, they do not want to ask you for it again but instead want to utilize the information you have already provided. This, of course, is contrasted with asking you for information each time, which is seen as a path with increased friction that could potentially cause you to abandon the journey.
What often gets lost in the desire to improve the user experience or make contextually relevant information available at the point of need, are a person’s deeply held views on what is personal data, how it can be shared and used with informed consent, and the laws and regulations that are relevant to the domain.
Whenever this topic comes up, I often go back and re-read the “7 Privacy-Embedded Laws of Identity” (PDF). These are a variation of the “7 Laws of Identity” (PDF) which were developed collaboratively by Kim Cameron of Microsoft. That work was in turn taken and infused with additional privacy aspects by the Information and Privacy Commissioner of Ontario, Canada.
In particular the following are directly relevant to this topic:
- Personal Control and Consent- “Technical identity systems must only reveal information identifying a user with the user’s consent. Personal control is fundamental to privacy, as is freedom of choice. Consent is pivotal to both.Consent must be invoked in the collection, use and disclosure of one’s personal information. Consent must be informed and uncoerced, and may be revoked at a later date.”
- Minimal Disclosure for Limited Use: Data Minimization- “The identity metasystem must disclose the least identifying information possible, as this is the most stable, long-term solution. It is also the most privacy protective solution. The concept of placing limitations on the collection, use and disclosure of personal information is at the heart of privacy protection. To achieve these objectives, one must first specify the purpose of the collection and then limit one’s use of the information to that purpose. These limitations also restrict disclosure to the primary purpose specified, avoiding disclosure for secondary uses. The concept of data minimization bears directly upon these issues, namely, minimizing the collection of personal information in the first instance, thus avoiding the possibility of subsequent misuse through unauthorized secondary uses.”
- Justifiable Parties: “Need to Know” Access- “Identity systems must be designed so the disclosure of identifying information is limited to parties having a necessary and justfiable place in a given identity relationship. This is consistent with placing limitations on the disclosure of personal information, and only allowing access on a need-to-know basis. Only those parties authorized to access the data, because they are justfiably required to do so, are granted access.”
It is also important to keep in mind that when it comes to implementation there are a lot of details that still need to be worked out. Where and how does one implement informed consent? What about the cost of asking for the information each time and storing and managing the information in multiple places? etc.
RELATED INFO
This blog post first appeared on Anil John | Blog (https://blog.aniljohn.com). The opinions expressed here are my own and do not represent my employer’s view in any way.




