Future of Identity Management is… Now!
The Gartner/Burton Group conference has a very high signal to noise ratio and is one that I was fortunate to present at this year. I spoke in my role as the Technical Lead for DHS Science & Technology Directorate’s Identity Management Testbed about how we are taking the Federal ICAM Backend Attribute Exchange Interface and Architecture Specification from Profile to Usage.
The biggest buzz in the Identity Management track, where I spent most of my time, was around the “pull” based architecture that Bob Blakley and the rest of the Burton crew have been writing and speaking about for a while as being the future of Identity Management. The key take-away’s for me on this topic are:
- We are moving to an era where dynamic, contextual, policy driven mechanisms are needed to make real time access control decisions at the moment of need.
- The policy driven nature of the decisions require that the decision making capability be externalized from systems/applications/services and not be embedded within and that policy be treated as a first class citizen.
- The input to these decisions are based on information about the subject, information about the resource, environmental/contextual information, and more, that are often expressed as attributes/claims.
- These attributes/claims can reside in multiple authoritative sources where the authoritative-ness/relevance may be based on the closeness of a relationship that the keeper/data-steward of the source has with the subject.
- The relevant attributes are retrieved (“pulled”) from the variety of sources at the moment when a subject needs to access a system and are not pre-provisioned into the system.
- Standards! Standards! Standards! All of the moving parts here (finding/correlating attributes, movement of attributes across organizational boundaries, decision control mechanisms etc.) needs to be using standards based interfaces and technologies.
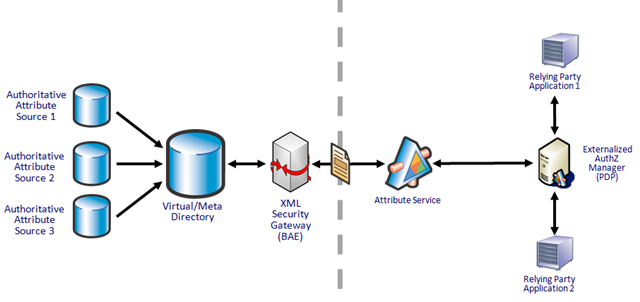
Potential implementation technologies proposed include virtual directories as mechanisms that can consolidate and correlate across multiple sources of attributes, standards such as LDAP(S), SAML and SPML as the plumbing standards, and External Authorization Mangers (“XACMLoids”) as decision engines.
What was interesting and relevant to me is the the US Federal Government via the ICAM effort as well as the Homeland Security, Defense and other communities have embraced this viewpoint for a while and are putting into place both the infrastructure to support it at scale, and have working implementations in use.
In particular my presentation was about how we are working an information sharing effort between two organizations who need to collaborate and share information in the event of a natural or man-made disaster where there is no way we could pre-provision users since we won’t know who those users are until they try to access systems. Our end-to-end implementation architecture really reflects pretty much everything noted in the Burton vision of the future. Relevant bits from the abstract:
The Backend Attribute Exchange (BAE) Interface and Architecture Specifications define capabilities that provide for both the real time exchange of user attributes across federated domains using SAML and for the batch exchange of user attributes using SPML.
The DHS Science & Technology (S&T) Directorate in partnership with the DOD Defense Manpower Data Center (DMDC), profiled SAML v2.0 as part of a iterative proof of concept implementation. The lessons learned and the profiles were submitted to the Federal CIO Council's Identity, Credentialing and Access Management (ICAM) Sub-Committee and are now part of the Federal Government's ICAM Roadmap as the standardized mechanism for Attribute Exchange across Government Agencies […]
This presentation will provide an overview of the BAE profiling effort, technical details regarding the choices made, vendor implementations, usage scenarios and discuss extensibility points that make this profile relevant to Commercial as well as Federal, State, Local and Tribal Government entities.
DHS S&T Presentation at Burton Group Catalyst
In our flow there is a clear separation of concerns between Authentication and Authorization and in the language of my community, the subject that is attempting to access the Relying Party application is an “Unanticipated User” i.e. a subject that is from outside that organization who has NOT been provisioned in the RP Application.
- There is a organizational access control policy that is externalized from the application via the Externalized Authorization Manager (EAM) that is dynamic in nature (“Allow access to user if user is from organization X, has attributes Y and Z and the current environment status is Green”).
- The subject is identified as being from outside the organization, is authenticated and an account is created in the system. The subject has no roles, rights or privileges within the system.
- The EAM pulls the attributes that are needed from external (to organization) sources to execute the access control policy and based on a permit decision grants access to resources that are allowed by policy.
All of this, BTW, is taking place using existing standards such as SAML and XACML and technologies such as Virtual Directories, XML Security Gateways, Externalized Access Management solutions etc. This works now using existing technology and standards and gets us away from the often proprietary, connector-driven, provisioning-dependent architectures and moves us to something that works very well in a federated world.
To us this is not the future of Identity Management. This is Now!
This blog post first appeared on Anil John | Blog (https://blog.aniljohn.com). The opinions expressed here are my own and do not represent my employer’s view in any way.




