Proxy Architecture
These days, [proxy/broker/hub/exchange architecture often comes up when discussing public sector service delivery][1]. A related topic is [component identity services][2]. And all of that is wrapped up around the ongoing discussion around value propositions, security, privacy, risk, and liability. These are some initial thoughts on bringing some of those topics together.
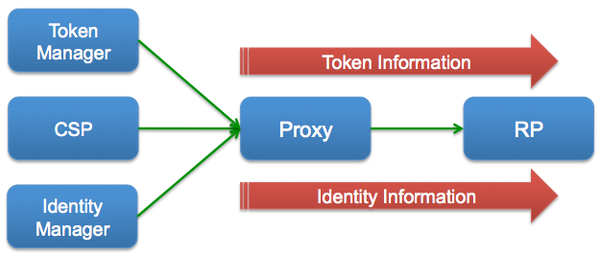
The typical model that I see associated with a proxy deployment is one I will call a Unified Proxy, in which the brokering of both the token information and the identity information is done by the same entity:
| Benefits | Challenges |
|---|---|
|
|
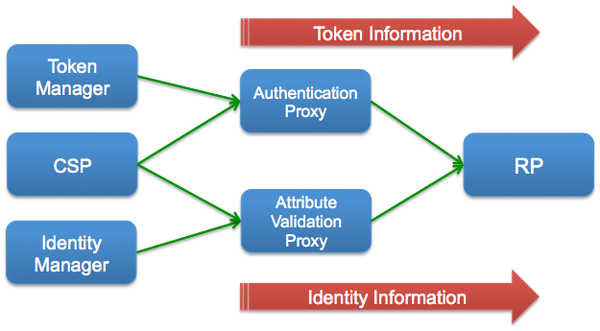
Another alternative is what I will call a Split Proxy, in which there is a physical (and not just logical) separation between the brokering of the token information and the brokering of the identity information:
| Benefits | Challenges |
|---|---|
|
|
This blog post first appeared on Anil John | Blog (https://blog.aniljohn.com). The opinions expressed here are my own and do not represent my employer’s view in any way.


 I am a public interest technologist. I help organizations and leaders gain clarity and understanding on complex architecture, information security, privacy practices, and market dynamics, so they can enable secure, trustworthy digital services.
I am a public interest technologist. I help organizations and leaders gain clarity and understanding on complex architecture, information security, privacy practices, and market dynamics, so they can enable secure, trustworthy digital services. 

